Linus Tech Tips Youtube Channel hacked. Here's why you don't need to worry as a GNU Linux user

Linus Tech Tips and their media house's other Youtube channels were hacked using session tokens with malware disguised as PDF.
In a sad turn of events, Linus Media House has been hacked and its Youtube channels temporarily hijacked by a third party.
Canadian Youtuber Linus Sebastian told us it was an exercise and a learning experience worth sharing with the community to keep everyone safe by working together and educating each other about the issue. He ended up blaming Youtube's operational security policy for this first-hand experience.
He didn't deny the help he received from the Youtube team, or the fact that his own staff weren't properly trained to work for a major media company that preaches operational security to people to keep their stuff safe from random hackers.
Linus Tech Tips said in a Youtube video that one of their employees opened a PDF and it hacked the browser's data - giving the intruders access to the web browser's 'session tokens' - which led to the hack.
I understand they were running Microsoft Windows.
Linus did his best to explain. But many questions remain unanswered.
Can this happen on a GNU Linux distribution?
Especially if the webmail software is running in Firefox, which runs in a container, i.e. a Snap or Flatpak application. Or if your mail client is a Snap or Flatpak application.
Yes, because they don't need access to your computer at all.
Being in a Snap means that they can't access any other data, but they can still access the browser data in the browser if you were running webmail.
Yes, if Firefox has the session cookies, and if you are opening the PDF with Firefox, and Firefox has an appropriate vulnerability. Of course it depends on the specific vulnerability.
But won't an anti-malware or scan tool or some other paid internet security application know that the PDF has malware? Do you think he used a good anti-malware solution?
I don't know what email provider they use or whether they host it themselves, but I can see from the DNS records of the Linus Media House website that they use Gmail. What about the virus scanning and advanced malware protection that Gmail offers?
It's possible the malware didn't install anything at all, so it depends on how it works. Let us assume that instead of installing something, it was an in-browser bug that revealed the session token, which the bad guy then copied.
If it was a PDF that was downloaded and opened, and your PDF reader was a Snap or Flatpak application, it wouldn't have been able to do anything like that.
As for anti-malware scanning, it might have caught it. But not necessarily. Malware authors are very good at getting around these things when they want to.
But remember, with PDF's, web browsers have readers built into the browser itself. So again, access is still there.
Theoretical security is very hard once you get to where a lot of attack vectors are. Basically, nobody who isn't a nation state actually locks everything down, because then they wouldn't be able to use the internet at all.
I think Linus mentioned something about a site-wide anti-malware solution, and a follow-up procedure that wasn't in place - so I think it was detected.
Since the PDF was actually scanned before it was opened, what could have been done differently to prevent it?
Can this happen to you on a popular GNU Linux distribution like Debian?
Usually not, because most (virtually all I've seen) free/libre PDF readers don't run drive-by programs embedded/attached to documents by default.
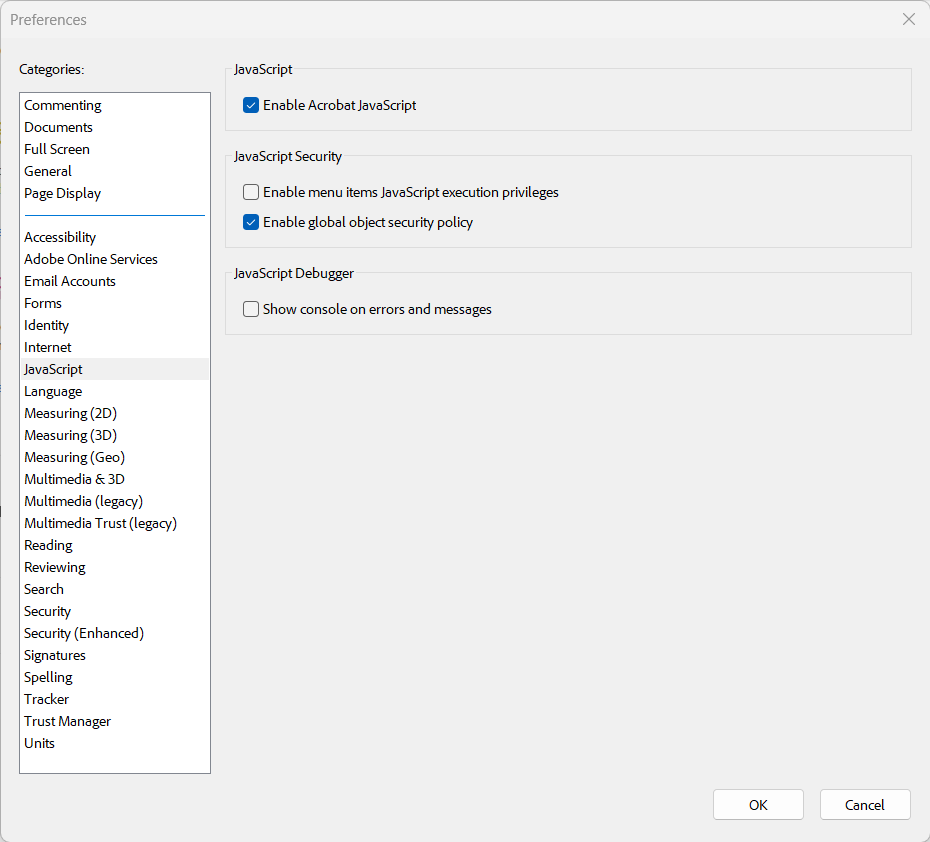
For proprietary software, they do; I know this because when I have had to deal with proprietary Adobe Acrobat installs (usually on a proprietary OS like Microsoft Windows), I have had to dig through configuration options to explicitly disable them.
I have also heard from Outlook [email client software] users that Microsoft Outlook (at least at one point) also did something equally silly, like opening attachments with shell action (which means "run" to programs) automatically by default when you open an email to read; which is outrageous.
I have no insight beyond what is reported in the news; I am just saying what I can see about the risks of proprietary versus free/libre installations in terms of drive-by programs that could lead to such a security breach.
Session hijacking in general is more difficult under GNU Linux
If they were running "Debian or Trisquel", the first thing is that malware (whether they use actual security flaws or operate in Trojan-like fashion) is usually written to target low-hanging (and abundant) fruit, which means Microsoft Windows (and common programs installed under it).
So the attacker's first hurdle, if the target is running a GNU/Linux installation, is that the attached program would not run.
Which usually means crisis averted.
But the hackers apparently knew which operating system a major Canadian media company was running. It is simply a popular choice, they could blindly guess and be right. And note that obscurity is not the only hurdle.
For example, if you send me a PDF malware in an email and I download it from my web browser and scan it with the extension from Virustotal - if it detects 0 issues there, I open it, the PDF itself opens in a web browser (as PDF reader) or my standalone PDF reader outside the web browser.
On Windows based systems there is a (mis)feature that is enabled by default to hide known file extensions from the file list of the file manager (Windows Explorer).
Can a web browser run executable files?
Yes, web browsers run executable JavaScript automatically and silently.
A web browser can certainly run executables of a certain type in HTML mode, but not so much in PDF mode.
Anyway, the exploit in question came from email, and because it's a big company (not some random individual's tech magazine), it's much less likely that the browser itself is involved in the initial malware delivery.
It's much more likely that the employee used the actual email client; then tried to open the PDF from the file manager.
If you have access to the Adobe Acrobat Reader installation, go to its configuration screen and look for "JavaScript" in the settings.
A defect in the Windows file manager about hidden extensions. This has also helped malware writers.
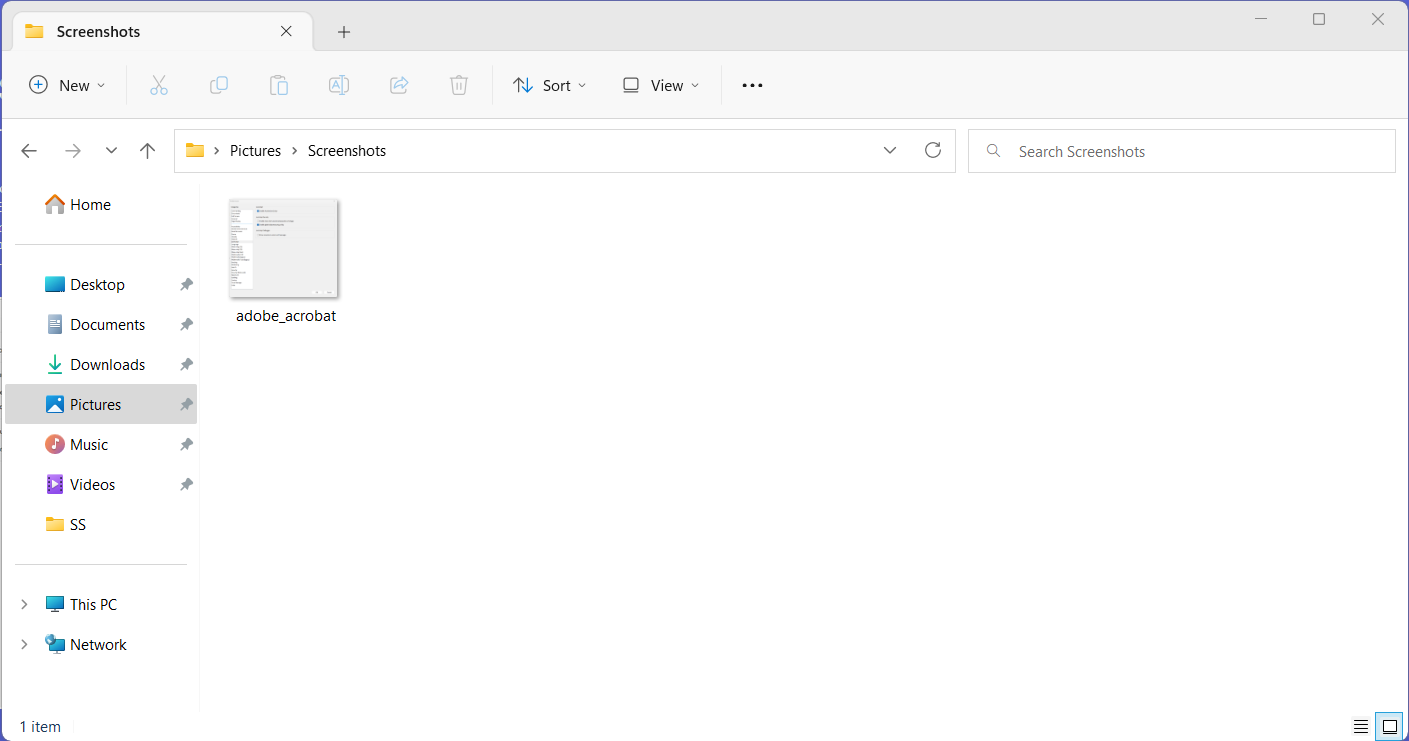
What could have been different in Nautilus on Debian?
Because Unix-like file managers don't do that. File extensions are shown there.
So in Windows, if you saved an attachment from an email client, it would show up in the file manager as something like "contract".
And the user would look at its icon to see what type of file it was. This is where the attacker exploits the target.
If the file "contract" is displayed like this, with paper and a PDF-like ribbon icon, there are two possibilities:
A. It was actually named "contract.pdf" and contains real PDF content that can be read with a PDF reader.
B. It was actually called "contract.exe", with its own icon mimicking Adobe Acrobat's file icon, and contains a Trojan horse executable.
Inexperienced users would assume it was A. Even if you know all the problems, even an "experienced" user might not notice if they forgot to turn off the file extension hiding feature.
So one way an attacker might exploit this is to send an email detailing a "potential business opportunity" with B as an attachment.
Do they write the code to bypass popular anti-malware software?
So the victim looked at the email, saw a good business opportunity, saved the attachment and opened it in a hurry.
Linus said there was actually a malware warning and the procedure wasn't followed, I'm not sure if it was before or after the email was opened.
It's fine to use a malware scanner (whatever brand/multi-brand it is), but always remember that a scanner cannot detect brand-new malware, or non-widespread malware written specifically for one target.
In any case, the file extension mishap could have been avoided (there are a couple of settings in Explorer's Folder Options).
In practice, however, it requires knowledge and patience to know the settings, and it requires a setup technician (or mass-deployer) to go through each option and set it to a reasonable value.
In reality, this is above the pay grade of the average Windows technician.
Did you hear the news the other day that Microsoft's official support technician "fixed" the Windows activation problem by running 3rd party cracks?
I can't believe it.
— TCNO/TroubleChute (@TCNOco) March 11, 2023
My official Microsoft Store Windows 10 Pro key wouldn't activate. Support couldn't help me yesterday.
Today it was elevated. Official Microsoft support (not a scam) logged in with Quick Assist and ran a command to activate windows.
BRO IT'S A CRACK
NO CAP pic.twitter.com/0vcRGu9PDE
That showed the level of (in)competence of such support people.
Well, running the crack might show competence, since the "official" activation program probably doesn't work. It shows the incompetence of the actual developers.
Anyway, this "exploit" we are discussing is basically user error caused by Windows' exploitable defaults; and does not even involve drive-by execution at the PDF level yet.
From what I read in the news, it looked like it was just a user error, mostly due to Microsoft's exploitable defaults. So once the Trojan executable is run, it's over for them.
Suggestions
Regardless of the operating system you are using, I suggest you use a service like Virustotal, which helps you analyse a file (such as attachments you receive via email), URL, domain, IP address, using 70+ antivirus products, 10+ dynamic analysis sandboxes, and a myriad of other security tools, to give you a threat score and the context to understand it. This is the bare minimum that you need to do if you are going to download something from a source that you do not trust.
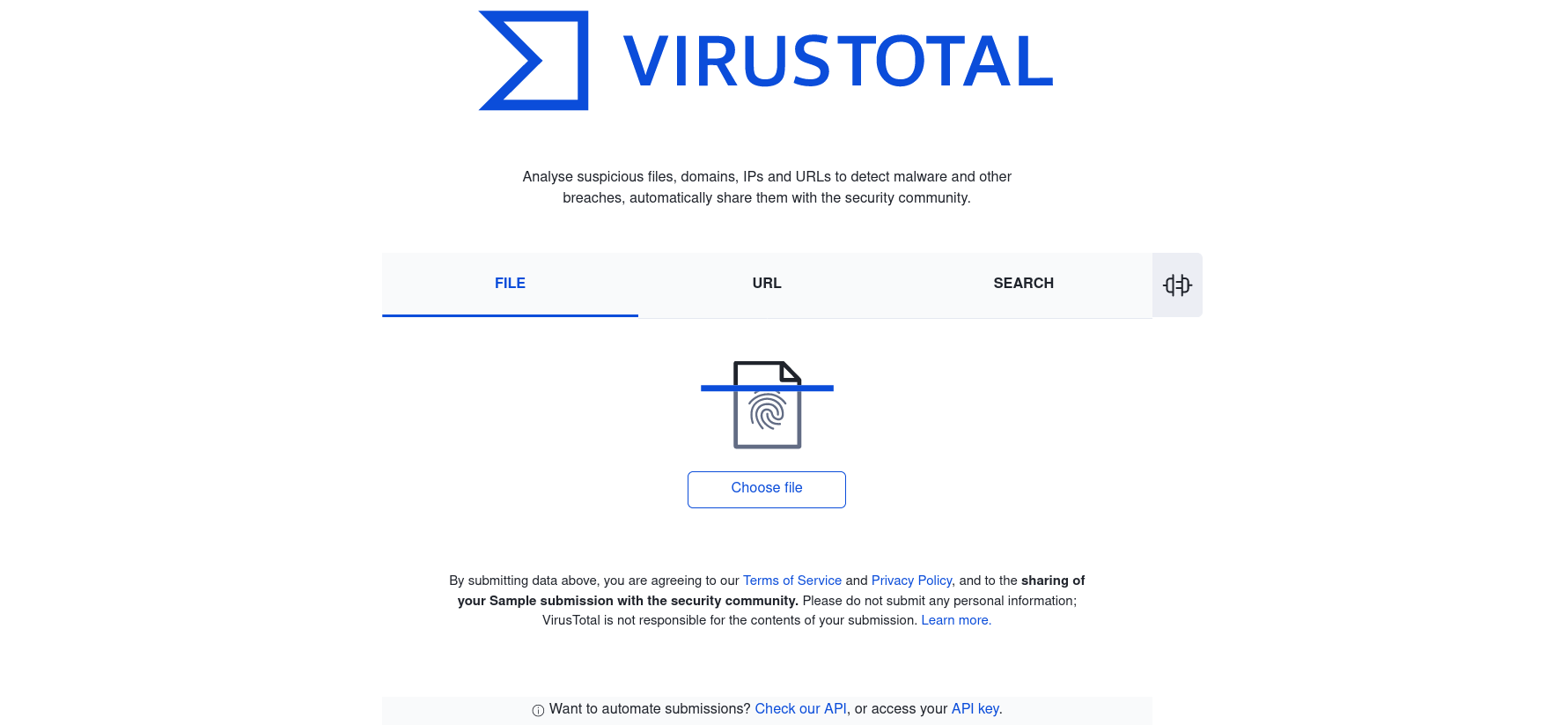
They also support an API where you can automate a lot of things. There are also desktop applications and browser plugins with features such as automatic scanning of all downloads.
Also, Linus Tech Tips, here is a free tech tip, run GNU Linux with a secure free/libre PDF reader or document reader in a container-style package like Snap or Flatpak.